What is rule-based detection when compared to statistical detection?
A.
proof of a user's identity
B.
proof of a user's action
C.
likelihood of user's action
D.
Dfalsification of a user's identity
proof of a user's action
Which two elements are used for profiling a network? (Choose two.)
A.
session duration
B.
total throughput
C.
running processes
D.
listening ports
E.
EOS fingerprint
listening ports
EOS fingerprint
Which evasion technique is indicated when an intrusion detection system begins receiving an abnormally high volume of scanning from numerous sources?
A.
resource exhaustion
B.
tunneling
C.
traffic fragmentation
D.
timing attack
resource exhaustion
Which attack is the network vulnerable to when a stream cipher like RC4 is used twice with the same key?
A.
forgery attack
B.
plaintext-only attack
C.
ciphertext-only attack
D.
meet-in-the-middle attack
ciphertext-only attack
What does cyber attribution identify in an investigation?
A.
exploit of an attack
B.
threat actors of an attack
C.
vulnerabilities exploited
D.
cause of an attack
threat actors of an attack
Which two elements of the incident response process are stated in NIST Special
Publication 800-61 r2? (Choose two.)
A.
detection and analysis
B.
post-incident activity
C.
vulnerability management
D.
risk assessment
detection and analysis
post-incident activity
Reference: https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-61r2.pdf
A security engineer has a video of a suspect entering a data center that was captured on the same day that files in the same data center were transferred to a competitor. Which type of evidence is this?
A.
best evidence
B.
prima facie evidence
C.
indirect evidence
D.
physical evidence
indirect evidence
Refer to the exhibit.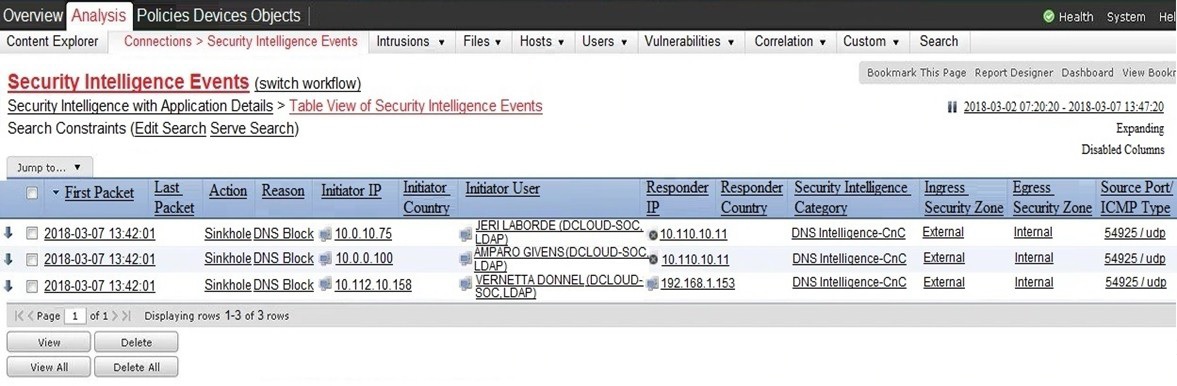
Which two elements in the table are parts of the 5-tuple? (Choose two.)
A.
A. First Packet
B.
Initiator User
C.
Ingress Security Zone
D.
Source Port
E.
Initiator IP
Source Port
Initiator IP
A network engineer discovers that a foreign government hacked one of the defense contractors in their home country and stole intellectual property. What is the threat agent in this situation?
A.
the intellectual property that was stolen
B.
the defense contractor who stored the intellectual property
C.
the method used to conduct the attack
D.
the foreign government that conducted the attack
the foreign government that conducted the attack
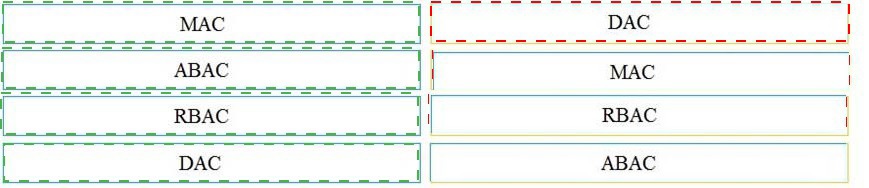
Drag and drop the access control models from the left onto the correct descriptions on the right.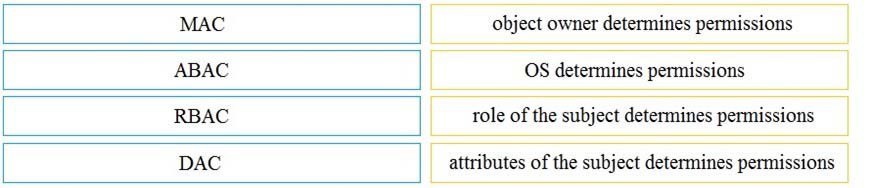
Which security principle requires more than one person is required to perform a critical task?
A.
least privilege
B.
need to know
C.
separation of duties
D.
due diligence
separation of duties
Which incidence response step includes identifying all hosts affected by an attack'?
A.
post-incident activity
B.
detection and analysis
C.
containment eradication and recovery
D.
preparation
post-incident activity
| Page 1 out of 34 Pages |
| 1234567891011 |
Real-World Scenario Mastery: Our 200-201 practice exam don't just test definitions. They present you with the same complex, scenario-based problems you'll encounter on the actual exam.
Strategic Weakness Identification: Each practice session reveals exactly where you stand. Discover which domains need more attention, before Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS) exam day arrives.
Confidence Through Familiarity: There's no substitute for knowing what to expect. When you've worked through our comprehensive 200-201 practice exam questions pool covering all topics, the real exam feels like just another practice session.