A user connected to Prisma Access reports that traffic intermittently is denied after matching a Catch-All Deny rule at the bottom and bypassing HIP-based policies.
Refreshing VPN connection restores the access.
What are two reasons for this behavior? (Choose two.)
A. "Collect HIP data' needs to be enabled in the configuration.
B. User mapping is learned from sources other than gateway authentication.
C. Firewall loses user mapping due to missed HIP report checks.
D. HIP-enforced policy is scheduled for certain hours of the day.
A customer is implementing Prisma Access (Managed by Strata Cloud Manager) to connect mobile users, branch locations, and business-to- business (B2B) partners to their data centers.
* The solution must meet these requirements:
* The mobile users must have internet filtering, data center connectivity, and remote site connectivity to the branch locations.
* The branch locations must have internet filtering and data center connectivity.
* The B2B partner connections must only have access to specific data center internally
developed applications running on non-standard ports.
* The security team must have access to manage the mobile user and access to branch
locations.
* The network team must have access to manage only the partner access.
Which two components can be provisioned to enable data center connectivity over the
internet? (Choose two.)
A. ZTNA Connector
B. SD-WAN Connector
C. Service connections
D. Colo-Connect
Which policy configuration in Prisma Access Browser (PAB) will protect an organization from malicious BYOD and minimize the impact on the user experience?
A. One that blocks file exchange
B. One for session recording
C. One that blocks elements such as screen scrapers
D. One that allows access to applications with data masking or watermarking
What is the impact of selecting the “Disable Server Response Inspection” checkbox after confirming that a Security policy rule has a threat protection profile configured?
A. Only HTTP traffic from the server to the client will bypass threat inspection.
B. The threat protection profile will override the 'Disable Server Response Inspection1 only for HTTP traffic from the server to the client.
C. All traffic from the server to the client will bypass threat inspection.
D. The threat protection profile will override the 'Disable Server Response Inspection1 for all traffic from the server to the client.
Which feature can help address a customer concern about the length of time it takes to update their SaaS-allowed IP addresses while onboarding to Prisma Access?
A. Dynamic IP pooling
B. DNS-based load balancing
C. Traffic steering
D. Dedicated IP addresses
Based on the image below, which two statements describe the reason and action required to resolve the errors? (Choose two.)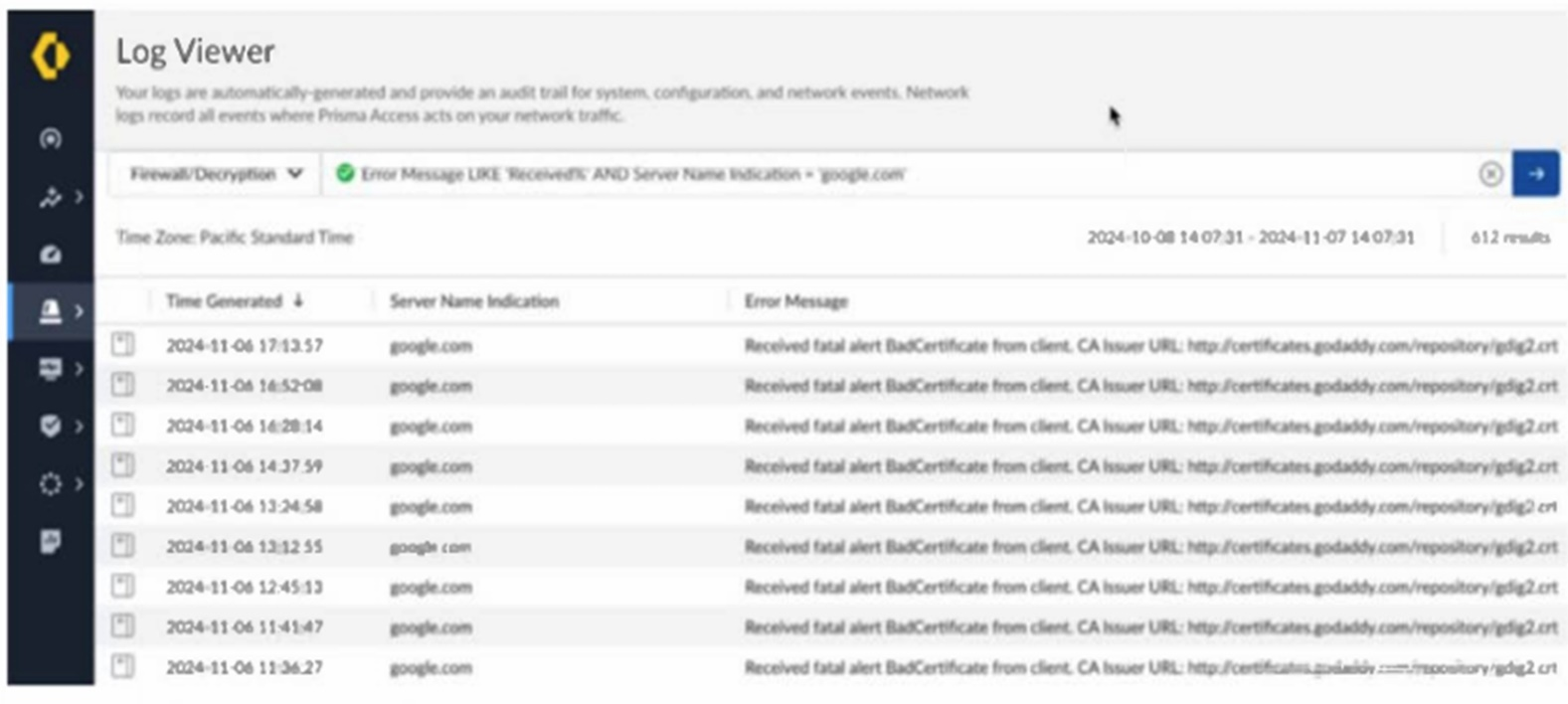
A. The client is misconfigured.
B. Create a do not decrypt rule for the hostname “google.com.”
C. The server has pinned certificates.
D. Create a do not decrypt rule for the hostname “certificates.godaddy.com.”
A company has a Prisma Access deployment for mobile users in North America and Europe. Service connections are deployed to the data centers on these continents, and the data centers are connected by private links.
With default routing mode, which action will verify that traffic being delivered to mobile users traverses the service connection in the appropriate regions?
A. Configure BGP on the customer premises equipment (CPE) to prefer the assigned community string attribute on the mobile user prefixes in its respective Prisma Access region.
B. Configure each service connection to filter out the mobile user pool prefixes from the other region in the advertisements to the data center.
C. Configure BGP on the customer premises equipment (CPE) to prefer the MED attribute on the mobile user prefixes in its respective Prisma Access region.
D. Configure each service connection to prepend the BGP ASN five times for mobile user pool prefixes originating from the other region.
When using the traffic replication feature in Prisma Access, where is the mirrored traffic directed for analysis?
A. Specified internal security appliance
B. Dedicated cloud storage location
C. Panorama
D. Strata Cloud Manager (SCM)
A customer using Prisma Access (Managed by Panorama) wants to monitor traffic patterns across all remote networks and use Strata Logging Service to gather insights on network usage. An engineer notices that some network data is missing from the Application Command Center (ACC).
What should the engineer do to ensure complete data visibility?
A. Reconfigure the Prisma Access remote networks to log directly to Panorama instead of using Strata Logging Service.
B. Verify that the Panorama web interface has been configured to aggregate logs from both the Panorama data and RN-SPNs.
C. Enable the Use Data for Pre-Defined Reports' setting in the Logging and Reporting configuration on Panorama.
D. Ensure that log forwarding profiles are applied to all Prisma Access policies and directed to Strata Logging Service.
An intern is tasked with changing the Anti-Spyware Profile used for security rules defined in
the GlobalProtect folder. All security rules are using the Default Prisma Profile. The intern
reports that the options are greyed out and cannot be modified when selecting the Default
Prisma Profile.
Based on the image below, which action will allow the intern to make the required
modifications?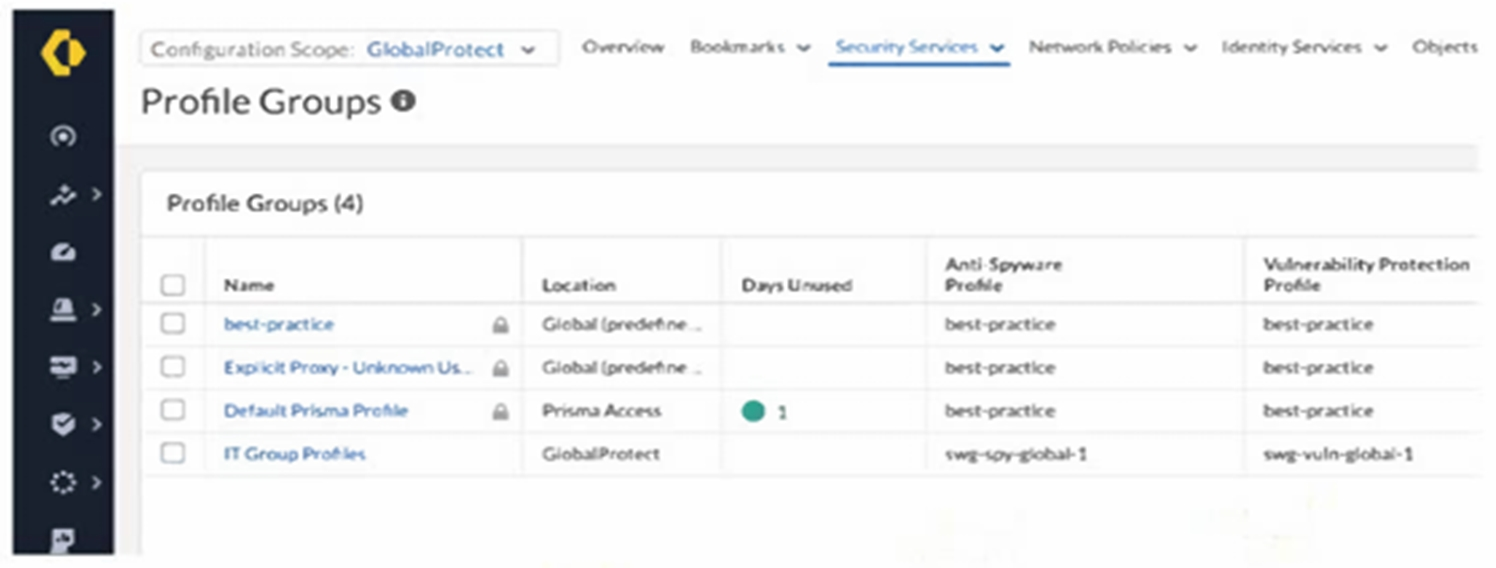
A. Request edit access for the GlobalProtect scope.
B. Change the configuration scope to Prisma Access and modify the profile group.
C. Create a new profile, because default profile groups cannot be modified.
D. Modify the existing anti-spyware profile, because best-practice profiles cannot be removed from a group.
A company has four branch offices between Canada Central and Canada East which use the same IPSec termination node and have QoS configured with customized bandwidth per site. An engineer wants to onboard a new branch office on the same IPSec termination node.
What is the QoS behavior for the new branch office?
A. Automatically distributed to 25% for each site
B. Unallocated until manually assigned
C. Automatically distributed to 20% for each site
D. Cannot be added to existing QoS configuration
Strata Logging Service is configured to forward logs to an external syslog server; however, a month later, there is a disruption on the syslog server.
Which action will send the missing logs to the external syslog server?
A. Configure a replay profile with the affected time range and associate it with the affected syslog server profile.
B. Delete the affected syslog server profile and create a new one.
C. Export the logs from Strata Logging Service, and then manually import them to the syslog server.
D. Configure a log filter under the syslog server profile with the affected time range.
| Page 1 out of 5 Pages |
| 12 |
Real-World Scenario Mastery: Our SSE-Engineer practice exam don't just test definitions. They present you with the same complex, scenario-based problems you'll encounter on the actual exam.
Strategic Weakness Identification: Each practice session reveals exactly where you stand. Discover which domains need more attention, before Palo Alto Networks Security Service Edge Engineer exam day arrives.
Confidence Through Familiarity: There's no substitute for knowing what to expect. When you've worked through our comprehensive SSE-Engineer practice exam questions pool covering all topics, the real exam feels like just another practice session.