Which two statements are correct about security zones? (Choose two.)
A. An interface can exist in multiple security zones.
B. Interfaces in the same security zone must share the same routing instance.
C. Interfaces in the same security zone must use separate routing instances.
D. A security zone can contain multiple interfaces.
Which two statements are correct about security zones and functional zones? (Choose two.)
A. Traffic entering an interface in a functional zone cannot exit any other transit interface.
B. Traffic entering transit interfaces can exit an interface in a functional zone.
C. Traffic entering an interface in a functional zone can exit any other transit interface.
D. Traffic entering transit interfaces cannot exit an interface in a functional zone.
Click the Exhibit button.
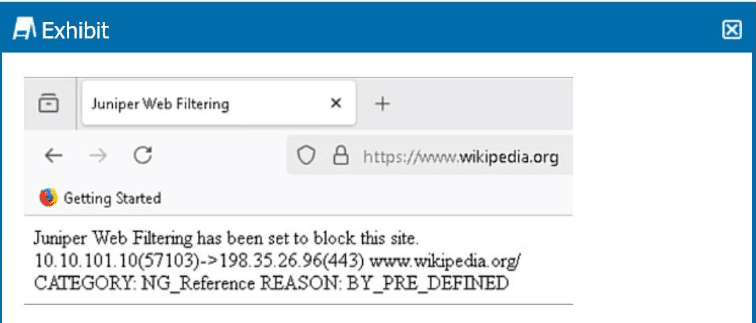 Referring to the exhibit, which two statements are correct? (Choose two.)
Referring to the exhibit, which two statements are correct? (Choose two.)
A. The URL matches a predefined Web filtering category.
B. The NextGen Web Filtering type is being used.
C. The SRX firewall does not have an SSL proxy configuration.
D. This is a custom Web filtering block message.
You are asked to reduce security configuration complexity on your external facing firewalls. You notice that a previous administrator included hundreds of private subnet NAT rules covering various RFC1918 addresses. You want to replace all these rules with a single rule covering all RFC1918 addresses. Which rule would you use in this scenario?
A. set security nat source rule-set private-to-pub rule RFC1918 match source-address [10.0.0.0/8 192.168.0.0/16 172.16.0.0/12]
B. set security nat source rule-set private-to-pub rule RFC1918 match source-address [10.0.0.0/8 192.16.0.0/12 172.168.0.0/16]
C. set security nat source rule-set private-to-pub rule RFC1918 match source-address [10.0.0.0/8 172.168.0.0/16 192.0.2.0/24 203.1.113.0/24]
D. set security nat source rule-set private-to-pub rule RFC1918 match source-address [10.0.0.0/8 192.168.0.0/16 172.16.0.0/12 192.0.2.0/24]
Click the Exhibit button.
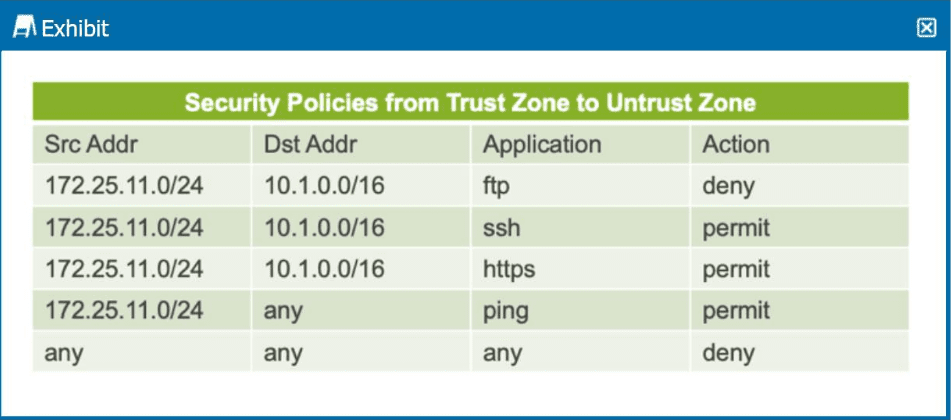
The exhibit shows a table representing security policies from the trust zone to the untrust
zone.
In this scenario, which two statements are correct? (Choose two.)
A. SSH requests from the source IP address of 172.25.11.10 are permitted to the destination IP address of 10.1.0.10.
B. Ping command requests from the source IP address of 172.25.11.100 are denied to the destination IP address of 10.1.0.10.
C. FTP requests from the source IP address of 10.1.0.10 are permitted to the destination IP address of 172.25.11.100.
D. FTP requests from the source IP address of 172.25.11.11 are denied to the destination IP address of 10.1.0.10.
You are asked to enable trace options to debug the packet flow. In this scenario, which flag would you configure at the [edit security flow traceoptions] hierarchy?
A. packet-dump
B. general
C. state
D. basic-datapath
In which order does Junos OS process the various forms of NAT?
A. static NAT, destination NAT, source NAT
B. destination NAT, source NAT, static NAT
C. source NAT, static NAT, destination NAT
D. source NAT, destination NAT, static NAT
Click the Exhibit button.
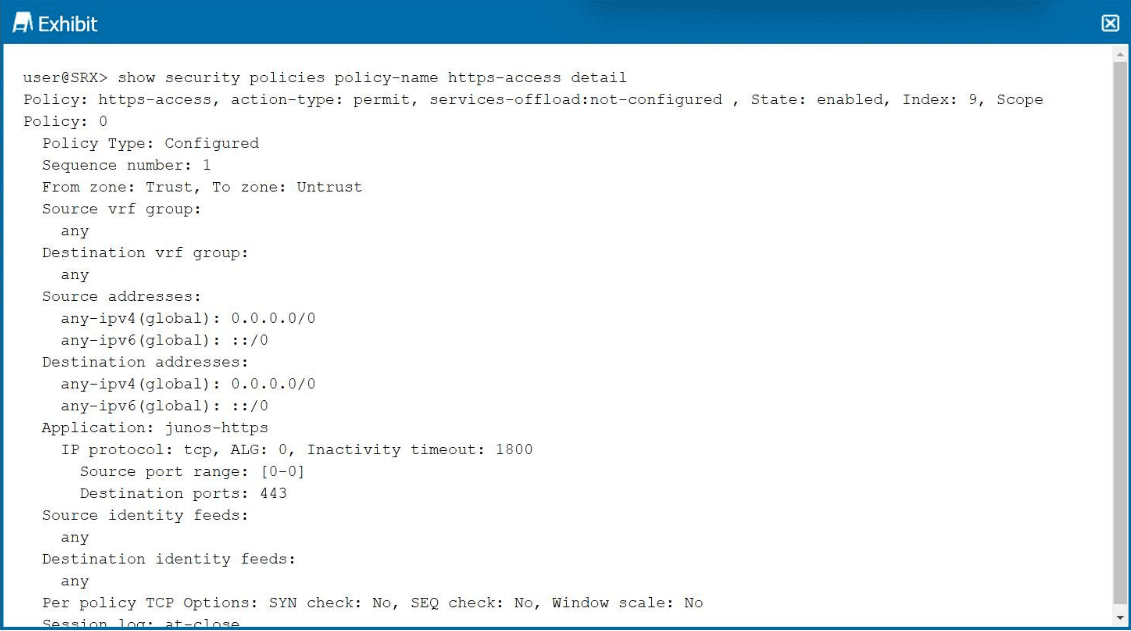
Referring to the exhibit, which two statements are correct? (Choose two.)
A. This security policy uses a non-default inactivity timeout.
B. This security policy is the second security policy in the list.
C. This security policy permits HTTPS traffic.
D. This security policy is a zone-based security policy.
What is the purpose of a feature profile in a UTM configuration?
A. It applies a UTM feature to a security policy.
B. It applies a UTM feature to protocol traffic.
C. It defines the operation of a specific UTM feature.
D. It defines an object list.
You are asked to create a security policy that controls traffic allowed to pass between the Internet and private security zones. You must ensure that this policy is evaluated before all other policy types on your SRX Series device. In this scenario, which type of security policy should you create?
A. routing policy
B. default policy
C. zone policy
D. global policy
Which two statements about global security policies are correct? (Choose two.)
A. The from-zone and to-zone contexts are not required for a global security policy.
B. Global security policies require specific zone contexts.
C. Global policies are processed before zone-based security policies.
D. You can use both zone-based security policies and global security policies at the same time.
What is transit traffic in the Junos OS?
A. It is traffic that is processed solely through the forwarding plane.
B. It is traffic that is rate-limited to prevent denial-of-service attacks.
C. It is traffic that is processed by the control plane.
D. It is traffic that requires special handling by the Routing Engine.
| Page 1 out of 6 Pages |
| 12 |
Real-World Scenario Mastery: Our JN0-232 practice exam don't just test definitions. They present you with the same complex, scenario-based problems you'll encounter on the actual exam.
Strategic Weakness Identification: Each practice session reveals exactly where you stand. Discover which domains need more attention, before Security, Associate (JNCIA-SEC) exam day arrives.
Confidence Through Familiarity: There's no substitute for knowing what to expect. When you've worked through our comprehensive JN0-232 practice exam questions pool covering all topics, the real exam feels like just another practice session.