A security analyst is developing a threat model that focuses on attacks associated with the
organization's storage products. The products:
• Are used in commercial and government user environments
• Are required to comply with crypto-export requirements
• Include both hardware and software components that are developed by external vendors
in Europe and Asia
Which of the following are the most important for the analyst to consider when developing
the model? (Select two).
A. Contractual obligations
B. Legal hold obligations
C. Trust boundaries
D. Cloud services enumeration
E. Supply chain access
F. Homomorphic encryption usage
A security analyst is reviewing the following authentication logs:
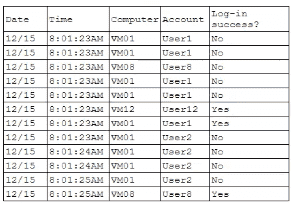
Which of the following should the analyst do first?
A. Disable User2's account
B. Disable User12's account
C. Disable User8's account
D. Disable User1's account
A company discovers intellectual property data on commonly known collaboration web
applications that allow the use of slide templates. The systems administrator is reviewing
the configurations of each tool to determine how to prevent this issue. The following
security solutions are deployed:
CASB
SASE
WAF
EDR
Firewall
IDS
SIEM
DLP endpoints
Which of the following should the administrator do to address the issue?
A. Enable blocking for all WAF policies.
B. Enforce a policy to block unauthorized web applications within CASB.
C. Create an alert within the SIEM for outgoing network traffic to the suspected website.
D. Configure DLP endpoints to block sensitive data to removable storage.
A water power generation plant fails a security inspection. The controllers are distributed across a river that is 0.5mi (0.8km) wide. The controllers are connected via HTTP to the shoreside master controller. The distributed controllers and the shoreside controller communicate over the internet using a cellular network. The company cannot encrypt control traffic because the systems will not tolerate the additional overhead. Which of the following strategies is the best way to reduce the risk of compromise?
A. Monitoring control traffic for command sequences with out-of-range or unexpected values
B. Disconnecting cellular radios in favor of shielded Cat 5e cables to each of the controllers
C. Reviewing the ladder logic on the controllers to determine whether unauthorized changes have been introduced
D. Deploying a dedicated base station and reducing the footprint with highly directional antennas
Operational technology often relies upon aging command, control, and telemetry subsystems that were created with the design assumption of:
A. operating in an isolated/disconnected system.
B. communicating over distributed environments
C. untrustworthy users and systems being present.
D. an available EtherneVIP network stack for flexibility.
E. anticipated eavesdropping from malicious actors.
During an incident response activity, the response team collected some artifacts from a compromised server, but the following information is missing:
• Source of the malicious files
• Initial attack vector
• Lateral movement activities
The next step in the playbook is to reconstruct a timeline. Which of the following best
supports this effort?
A. Executing decompilation of binary files
B. Analyzing all network routes and connections
C. Performing primary memory analysis
D. Collecting operational system logs and storage disk data
A security team determines that the most significant risks within the pipeline are: • Unauthorized code changes • The current inability to perform independent verification of software modules Which of the following best addresses these concerns?
A. Code signing
B. Digital signatures
C. Non-repudiation
D. Lightweight cryptography
After a company discovered a zero-day vulnerability in its VPN solution, the company plans to deploy cloud-hosted resources to replace its current on-premises systems. An engineer must find an appropriate solution to facilitate trusted connectivity. Which of the following capabilities is the most relevant?
A. Container orchestration
B. Microsegmentation
C. Conditional access
D. Secure access service edge
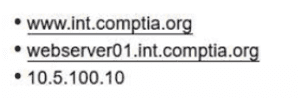
An administrator needs to craft a single certificate-signing request for a web-server
certificate. The server should be able to use the following identities to mutually authenticate
other resources over TLS:
• wwwJnt.comptia.org
• webserver01.int.comptia.org
•10.5.100.10
Which of the following certificate fields must be set properly to support this objective?
A. Subject alternative name
B. Organizational unit
C. Extended key usage
D. Certificate extension
A company wants to modify its process to comply with privacy requirements after an incident involving PII data in a development environment. In order to perform functionality tests, the QA team still needs to use valid data in the specified format. Which of the following best addresses the risk without impacting the development life cycle?
A. Encrypting the data before moving into the QA environment
B. Truncating the data to make it not personally identifiable
C. Using a large language model to generate synthetic data
D. Utilizing tokenization for sensitive fields
A security architect is troubleshooting an issue with an OIDC implementation. The architect
reviews the following configuration and errors:
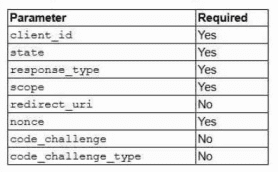
Error: Invalid authentication request code
Which of the following is the most likely cause of the error?
A. The redirect-url parameter is not in the allowed list of redirect hosts in the configuration.
B. Introspection is not enabled within the OIDC code implementation.
C. The encoding of the URL parameters on the proxy system is failing.
D. The state parameter is being reused within the authentication challenge.
E. OAuth 2.0 was unable to verify the lack of an interception attack.
A software vendor provides routine functionality and security updates to its global customer base. The vendor would like to ensure distributed updates are authorized, originate from only the company, and have not been modified by others. Which of the following solutions best supports these objectives?
A. Envelope encryption
B. File integrity monitoring
C. Application control
D. Code signing
| Page 12 out of 28 Pages |
| 8910111213141516 |
| CAS-005 Practice Test Home |
Real-World Scenario Mastery: Our CAS-005 practice exam don't just test definitions. They present you with the same complex, scenario-based problems you'll encounter on the actual exam.
Strategic Weakness Identification: Each practice session reveals exactly where you stand. Discover which domains need more attention, before CompTIA SecurityX Certification exam day arrives.
Confidence Through Familiarity: There's no substitute for knowing what to expect. When you've worked through our comprehensive CAS-005 practice exam questions pool covering all topics, the real exam feels like just another practice session.