A company must meet the following security requirements when implementing controls in
order to be compliant with government policy:
• Access to the system document repository must be MFA enabled.
• Ongoing risk monitoring must be displayed on a system dashboard.
• Staff must receive email notifications about periodic tasks.
Which of the following best meets all of these requirements?
A. Implementing a GRC tool
B. Configuring a privileged access management system
C. Launching a vulnerability management program
D. Creating a risk register
A systems engineer is configuring SSO for a business that will be using SaaS applications for its remote-only workforce. Privileged actions in SaaS applications must be allowed only from corporate mobile devices that meet minimum security requirements, but BYOD must also be permitted for other activity. Which of the following would best meet this objective?
A. Block any connections from outside the business's network security boundary.
B. Install machine certificates on corporate devices and perform checks against the clients.
C. Configure device attestations and continuous authorization controls.
D. Deploy application protection policies using a corporate, cloud-based MDM solution.
An attacker infiltrated the code base of a hardware manufacturer and inserted malware before the code was compiled. The malicious code is now running at the hardware level across a number of industries and sectors. Which of the following categories best describes this type of vendor risk?
A. SDLC attack
B. Side-load attack
C. Remote code signing
D. Supply chain attack
A social media company wants to change encryption ciphers after identifying weaknesses
in the implementation of the existing ciphers. The company needs the new ciphers to meet
the following requirements:
• Be more CPU-efficient than previous ciphers.
• Require customers to use TLS 1.3 while broadcasting video or audio.
Which of the following is the best choice for the social media company?
A. IDEA-CBC
B. AES-GCM
C. ChaCha20-Poly1305
D. Camellia-CBC
A malware researcher has discovered a credential stealer is looking at a specific memory register to harvest passwords that will be used later for lateral movement in corporate networks. The malware is using TCP 4444 to communicate with other workstations. The lateral movement would be best mitigated by:
A. Configuring the CPU's NX bit
B. Enabling a host firewall
C. Enabling an edge firewall
D. Enforcing all systems to use UEFI
E. Enabling ASLR on the Active Directory server
A company's Chief Information Security Officer learns that the senior leadership team is traveling to a country accused of attempting to steal intellectual property saved on laptops. Which of the following is the best method to protect against this attack?
A. Configure Measured Boot to report any firmware changes.
B. Use sanitized devices with remote connections to VDI.
C. Deploy self-encrypting drives to protect company data.
D. Install tamper-evident stickers over any laptop screws.
After a cybersecurity incident, a security analyst was able to collect a binary that the
attacker used on the compromised server. Then the analyst ran the following command:
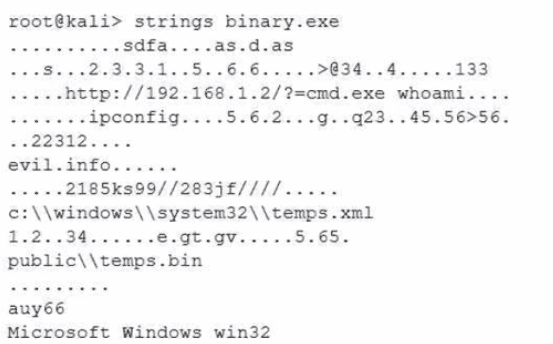
Which of the following options describes what the analyst is trying to do?
A. To reconstruct the timeline of commands executed by the binary
B. To extract loCs from the binary used on the attack
C. To replicate the attack in a secure environment
A company that uses several cloud applications wants to properly identify: All the devices potentially affected by a given vulnerability. All the internal servers utilizing the same physical switch. The number of endpoints using a particular operating system.Which of the following is the best way to meet the requirements?
A. SBoM
B. CASB
C. GRC
D. CMDB
Which of the following best describes a common use case for homomorphic encryption?
A. Processing data on a server after decrypting in order to prevent unauthorized access in transit
B. Maintaining the confidentiality of data both at rest and in transit to and from a CSP for processing
C. Transmitting confidential data to a CSP for processing on a large number of resources without revealing information
D. Storing proprietary data across multiple nodes in a private cloud to prevent access by unauthenticated users
A company finds logs with modified time stamps when compared to other systems. The security team decides to improve logging and auditing for incident response. Which of the following should the team do to best accomplish this goal?
A. Integrate a file-monitoring tool with the SIEM.
B. Change the log solution and integrate it with the existing SIEM.
C. Implement a central logging server, allowing only log ingestion.
D. Rotate and back up logs every 24 hours, encrypting the backups.
A security engineer must ensure that sensitive corporate information is not exposed if a company laptop is stolen. Which of the following actions best addresses this requirement?
A. Utilizing desktop as a service for all company data and multifactor authentication
B. Using explicit allow lists of specific IP addresses and deploying single sign-on
C. Deploying mobile device management and requiring stronger passwords
D. Updating security mobile reporting policies and monitoring data breaches
A security engineer receives the following findings from a recent security audit:
• Data should be protected based on user permissions and roles.
• User action tracking should be implemented across the network.
• Digital identities should be validated across the data access workflow.
Which of the following is the first action the engineer should take to address the findings?
A. Implement continuous and context-based authentication and authorization
B. Use an enhanced user credential provisioning workflow and data monitoring tools
C. Improve federation services for digital identities and data access
D. Deploy OpenID Connect for API authentication
| Page 11 out of 28 Pages |
| 789101112131415 |
| CAS-005 Practice Test Home |
Real-World Scenario Mastery: Our CAS-005 practice exam don't just test definitions. They present you with the same complex, scenario-based problems you'll encounter on the actual exam.
Strategic Weakness Identification: Each practice session reveals exactly where you stand. Discover which domains need more attention, before CompTIA SecurityX Certification exam day arrives.
Confidence Through Familiarity: There's no substitute for knowing what to expect. When you've worked through our comprehensive CAS-005 practice exam questions pool covering all topics, the real exam feels like just another practice session.