Topic 4: Mix Questions
You have a web app named WebApp1.
You create a web application firewall (WAF) policy named WAF1.
You need to protect WebApp1 by using WAF1.
What should you do first?
A. Deploy an Azure Front Door.
B. Add an extension to WebApp1.
C. Deploy Azure Firewall.
Your on-premises network contains an Active Directory Domain Services (AD DS) domain
and the devices shown in the following table.
You have a hybrid Microsoft Entra tenant that contains a synced user named User1.
You have an Azure subscription that contains the Azure Files shares shown in the following
table.
Used is assigned the Storage File Data SMB Share Contributor role tor storage1 and
storage2.
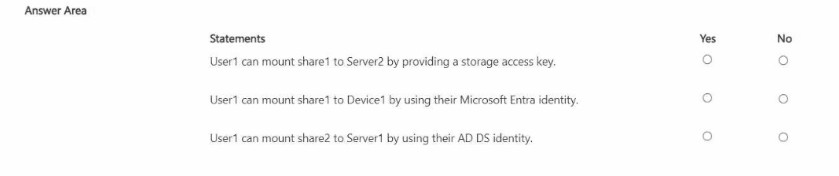
The Security settings for Share! are configured as shown in the following exhibit.
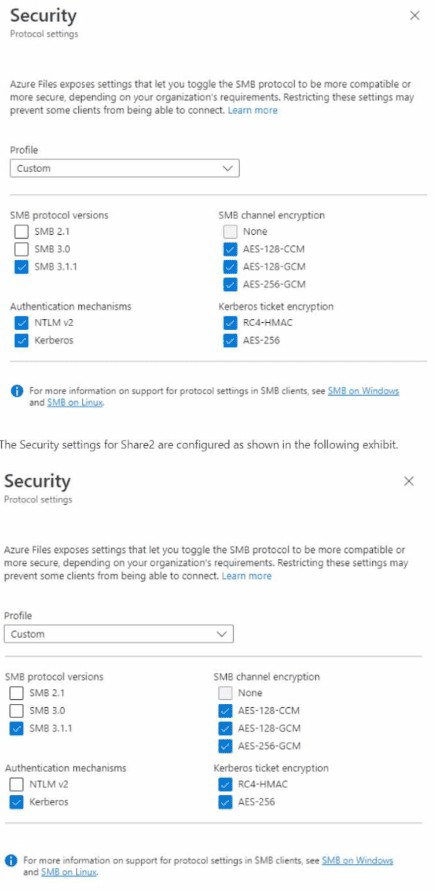
For each of the following statements, select Yes if the statement is true. Otherwise. Select
No.
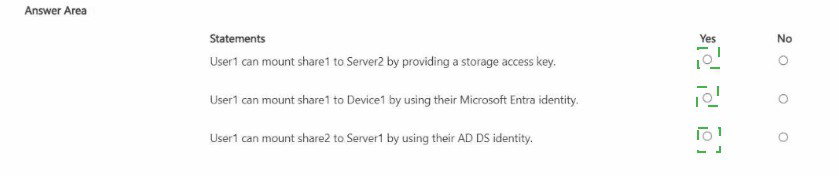
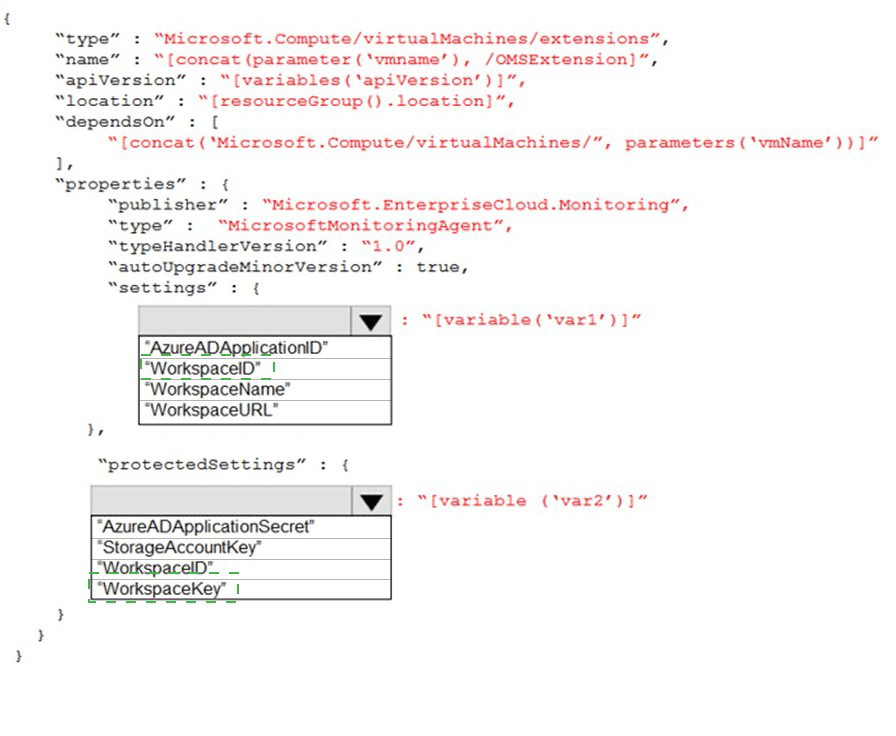
You plan to use Azure Log Analytics to collect logs from 200 servers that run Windows
Server 2016.
You need to automate the deployment of the Microsoft Monitoring Agent to all the servers
by using an Azure Resource Manager template.
How should you complete the template? To answer, select the appropriate options in the
answer area.
NOTE: Each correct selection is worth one point.
You have an Azure subscription that contains the resources shown in the following table.
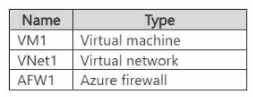
You need to configure AFW1 to only allow traffic from VM1 to storage accounts in the West
US Azure region. The solution must minimize administrative effort.
What should you configure?
A. a DNAT rule
B. a network rule
C. an SNAT private IP address range
D. an application rule
You are configuring and securing a network environment.
You deploy an Azure virtual machine named VM1 that is configured to analyze network
traffic.
You need to ensure that all network traffic is routed through VM1.
What should you configure?
A. a system route
B. a network security group (NSG)
C. a user-defined route
You are configuring an Azure Kubernetes Service (AKS) cluster that will connect to an
Azure Container Registry.
You need to use the auto-generated service principal to authenticate to the Azure
Container Registry.
What should you create?
A. an Azure Active Directory (Azure AD) group
B. an Azure Active Directory (Azure AD) role assignment
C. an Azure Active Directory (Azure AD) user
D. a secret in Azure Key Vault
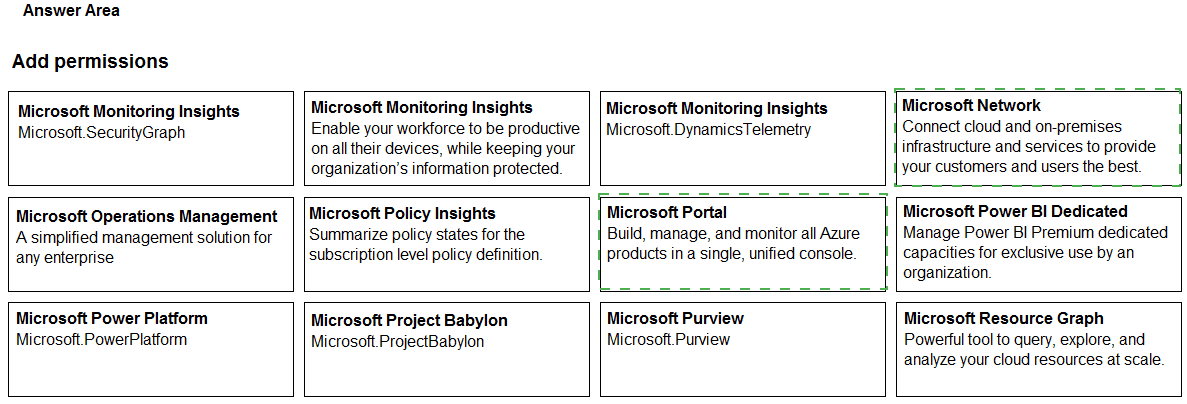
You have an Azure subscription that contains a user named User1. User1 is assigned the
Reader role for the subscription.
You plan to create a custom role named Role1 and assign Role1 to User1.
You need to ensure that User1 can create and manage application security groups by
using the Azure portal.
Which two permissions should you add to Role1? To answer, select the appropriate
permission in the answer area.
NOTE: Each correct selection is worth one point.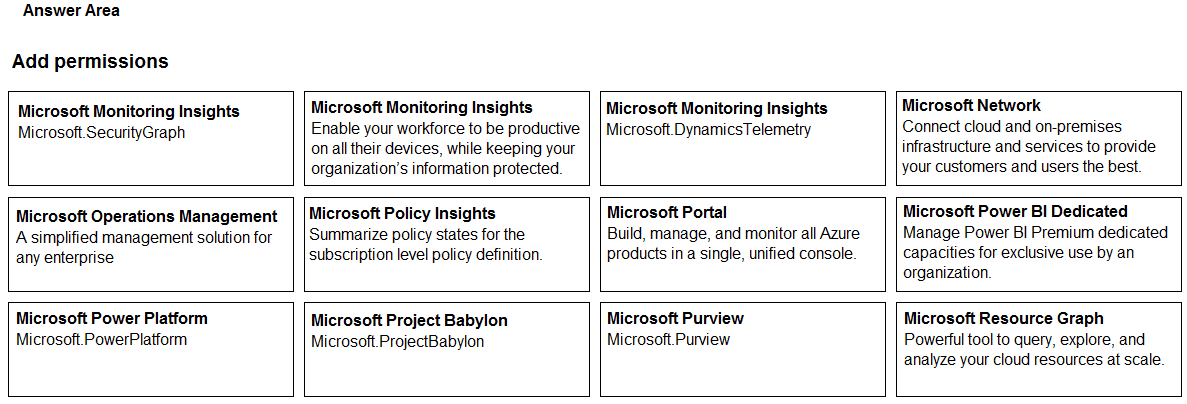
You have an Azure subscription that contains an Azure key vault. The role assignments for
the key vault are shown in the following exhibit.
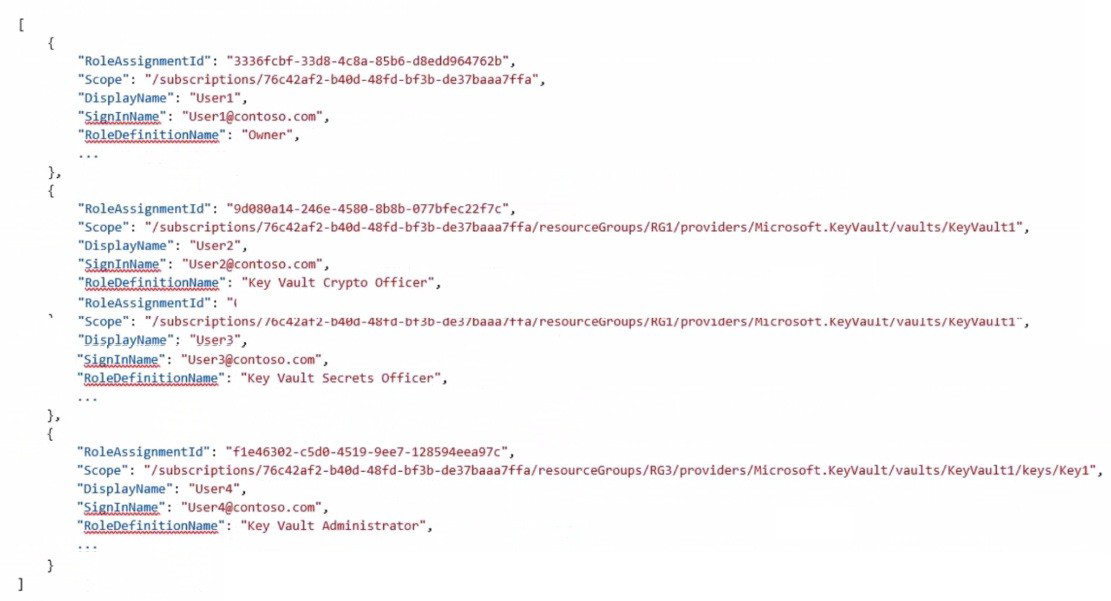
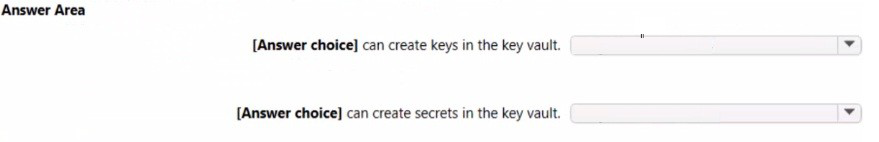
Use the drop-down menus to select the answer choice that completes each statement
based on the information presented in the graphic. NOTE: Each correct selection is worth
one point.
Answer: Answer: See the answer below at Explanation.
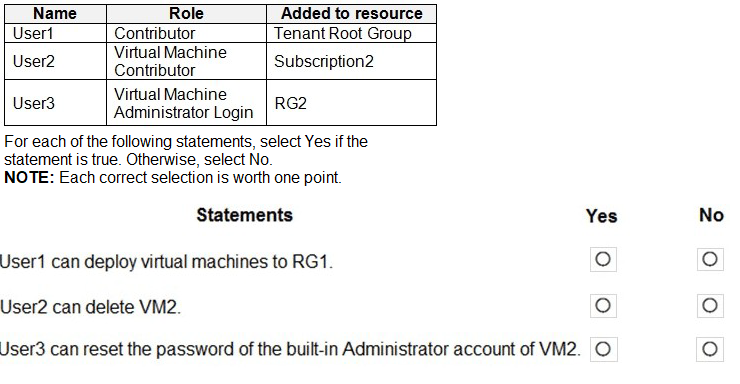
You have the hierarchy of Azure resources shown in the following exhibit.
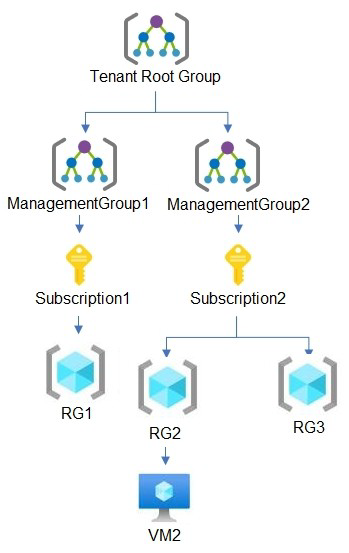
RG1, RG2, and RG3 are resource groups.
RG2 contains a virtual machine named VM1.
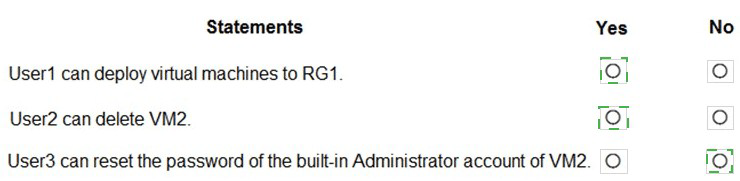
You assign role-based access control (RBAC) roles to the users shown in the following
table.
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some
question sets might have more than one correct solution, while others might not have a
correct solution.
After you answer a question in this section, you will NOT be able to return to rt As a result,
these questions will not appear in the review screen.
You have an Azure subscription named Sub1.
You have an Azure Storage account named Sa1 in a resource group named RG1.
Users and applications access the blob service and the file service in Sal by using several
shared access signatures {SASs) and stored access policies.
You discover that unauthorized users accessed both the rile service and the blob service.
You need to revoke all access to Sa1.
Solution: You regenerate the access keys.
Does this meet the goal?
A. Yes
B. No
You have an Azure subscription that uses Microsoft Defender for Cloud. You need to use Defender for Cloud to review regulatory compliance with the Azure CIS 1.4,0 standard. The solution must minimize administrative effort. What should you do first?
A. Assign an Azure policy.
B. Manually add the Azure CIS 1.4.0 standard.
C. Disable one of the Out of the box standards.
D. Add a custom initiative.
You have an Azure Active Din-dory (Azure AD) tenant named contoso.com that contains a user named User1. You plan to publish several apps in the tenant. You need to ensure that User1 can grant admin consent for the published apps. Which two possible user roles can you assign to User! to achieve this goal? Each correct answer presents a complete solution. NOTE: Each correct selection is worth one point.
A. Application developer
B. Security administrator
C. Application administrator
D. User administrator
E. Cloud application administrator
| Page 9 out of 42 Pages |
| Previous |