Topic 4: Mix Questions
You are collecting events from Azure virtual machines to an Azure Log Analytics
workspace.
You plan to create alerts based on the collected events.
You need to identify which Azure services can be used to create the alerts.
Which two services should you identify? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
A. Azure Monitor
B. Azure Security Center
C. Azure Analytics Services
D. Azure Sentinel
E. Azure Advisor
You have the Azure resource shown in the following table.
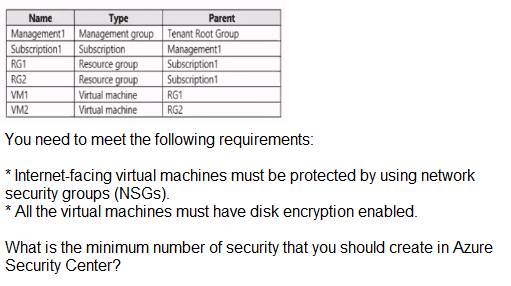
A. 1
B. 2
C. 3
D. 4
You have an Azure subscription that contains a storage account named storage1 and a
virtual machine named VM1.
VM1 is connected to a virtual network named VNet1 that contains one subnet and uses
Azure DNS.
You need to ensure that VM1 connects to storage1 by using a private IP address. The
solution must minimize administrative effort.
What should you do?
A. For storage1, disable public network access.
B. Create an Azure Private DNS zone.
C. On VNet1. create a new subnet.
D. For storage1, create a new private endpoint.
Note: This question is part of a series of questions that present the same scenario. Each
question in the series contains a unique solution that might meet the stated goals. Some
question sets might have more than one correct solution, while others might not have a
correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result,
these
questions will not appear in the review screen.
You have an Azure Subscription named Sub1.
You have an Azure Storage account named Sa1 in a resource group named RG1.
Users and applications access the blob service and the file service in Sa1 by using several
shared access
signatures (SASs) and stored access policies.
You discover that unauthorized users accessed both the file service and the blob service.
You need to revoke all access to Sa1.
Solution: You create a new stored access policy.
Does this meet the goal?
A. Yes
B. No
You have an Azure subscription that uses Microsoft Sentinel.
You need to create a Microsoft Sentinel notebook that will use the Guided Investigation -
Anomaly Lookup template.
What should you create first?
A. an analytics rule
B. a Log Analytics workspace
C. an Azure Machine Learning workspace
D. a hunting query
You are troubleshooting a security issue for an Azure Storage account. You enable the diagnostic logs for the storage account. What should you use to retrieve the diagnostics logs?
A. the Security & Compliance admin center
B. SQL query editor in Azure
C. File Explorer in Windows
D. AzCopy
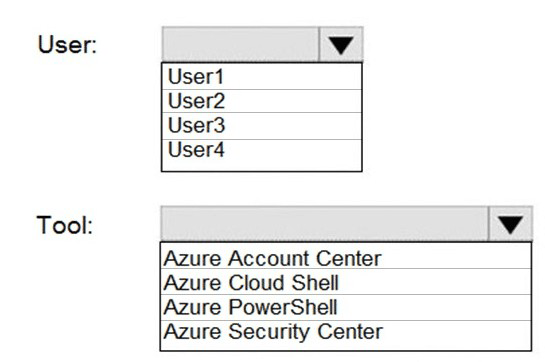
Your company has an Azure subscription named Subscription1 that contains the users
shown in the following table.
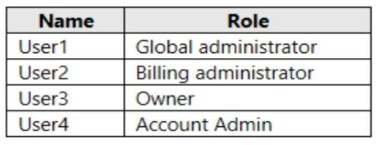
The company is sold to a new owner.
The company needs to transfer ownership of Subscription1.
Which user can transfer the ownership and which tool should the user use? To answer,
select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
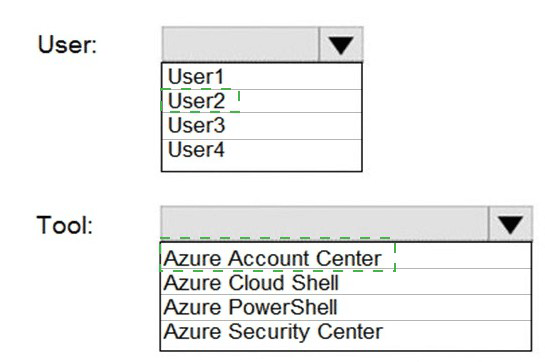
You have an Azure subscription that contains the users shown in the following table.
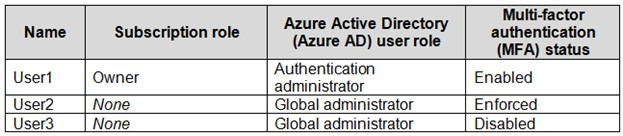
Which users can enable Azure AD Privileged Identity Management (PIM)?
A. User2 and User3 only
B. User1 and User2 only
C. User2 only
D. User1 only
Note: This question is part of a series of questions that present the same scenario. Each
question in the series contains a unique solution that might meet the stated goals. Some
question sets might have more than one correct solution, while others might not have a
correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result,
these questions will not appear in the review screen.
You use Azure Security Center for the centralized policy management of three Azure
subscriptions.
You use several policy definitions to manage the security of the subscriptions.
You need to deploy the policy definitions as a group to all three subscriptions.
Solution: You create a resource graph and an assignment that is scoped to a management
group.
Does this meet the goal?
A. Yes
B. No
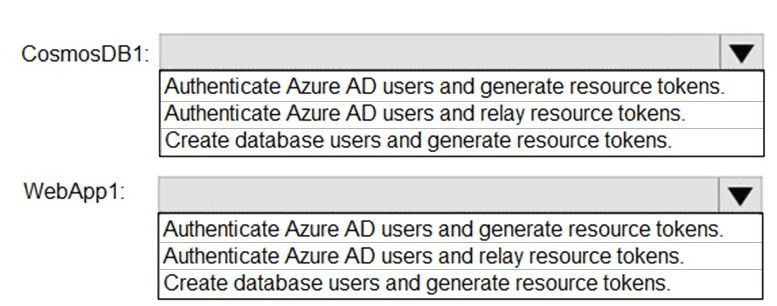
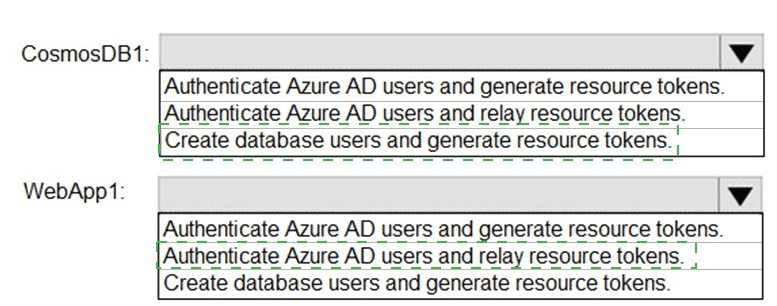
You have an Azure subscription named Sub1 that is associated to an Azure Active
Directory (Azure AD) tenant named contoso.com.
You plan to implement an application that will consist of the resources shown in the
following table.
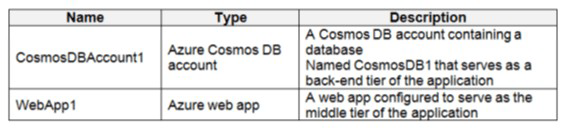
Users will authenticate by using their Azure AD user account and access the Cosmos DB
account by using resource tokens.
You need to identify which tasks will be implemented in CosmosDB1 and WebApp1.
Which task should you identify for each resource? To answer, select the appropriate
options in the answer area.
NOTE: Each correct selection is worth one point.
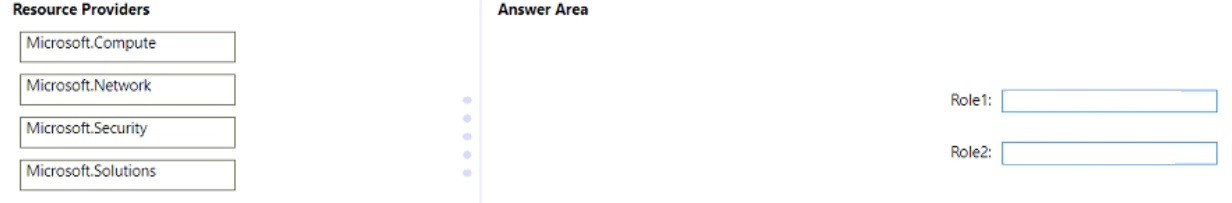
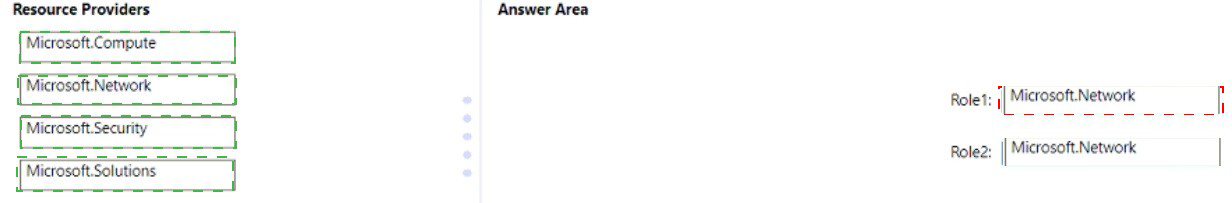
You have an Azure subscription.
You plan to create two custom roles named Role1 and Role2.
The custom roles will be used to perform the following tasks:
• Members of Role1 will manage application security groups.
• Members of Role2 will manage Azure Bastion.
You need to add permissions to the custom roles.
Which resource provider should you use for each role? To answer, drag the appropriate
resource providers to the correct roles. Each resource provider may be used once, more
than once, or not at all. You may need to drag the split bar between panes or scroll to view
content
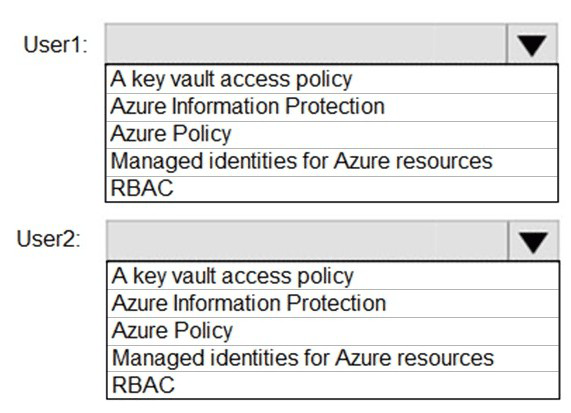
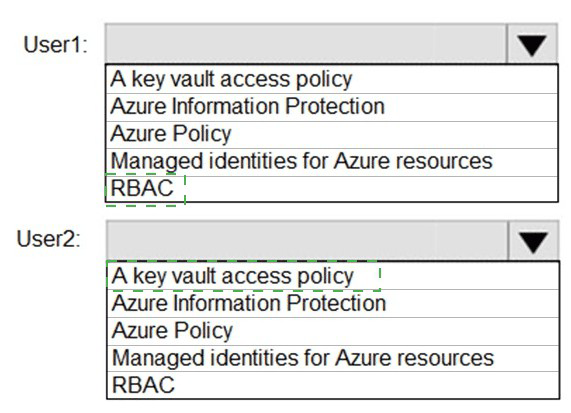
You have an Azure key vault.
You need to delegate administrative access to the key vault to meet the following
requirements:
Provide a user named User1 with the ability to set advanced access policies for
the key vault.
Provide a user named User2 with the ability to add and delete certificates in the
key vault.
Use the principle of least privilege.
What should you use to assign access to each user? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
| Page 8 out of 42 Pages |
| Previous |