Topic 4: Mix Questions
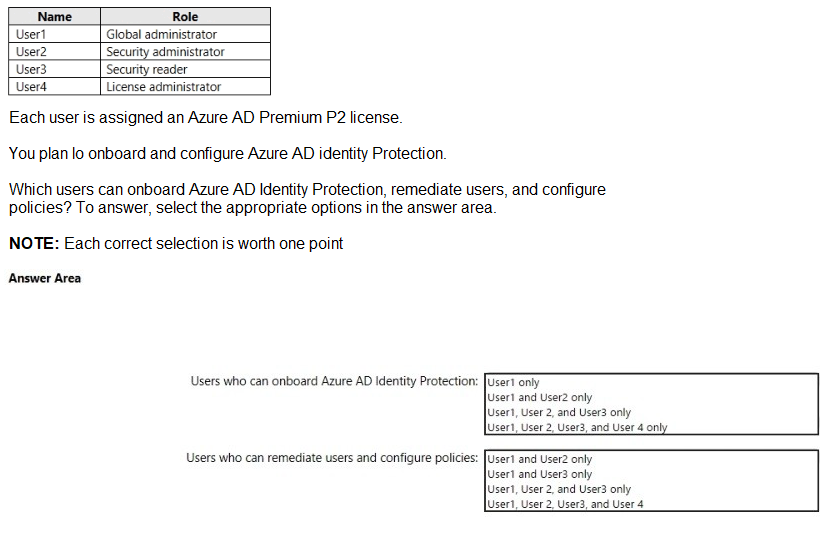
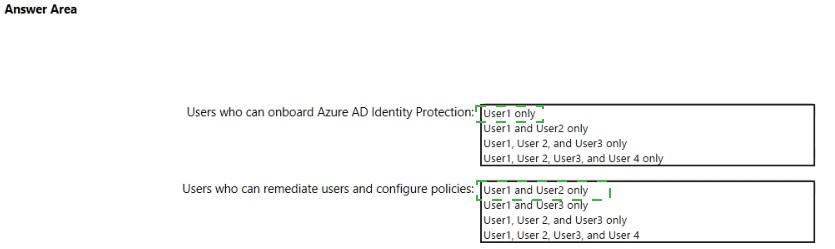
You have an Azure subscription named Sub 1 that is associated to an Azure Active Directory (Azure AD) tenant named contoso.com. The tenant contains the users shown in the following table.
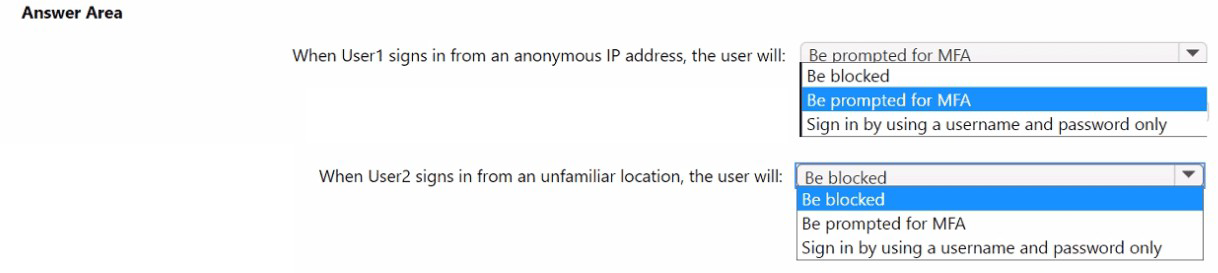
You have a Microsoft Entra tenant that contains the users shown in the following table.
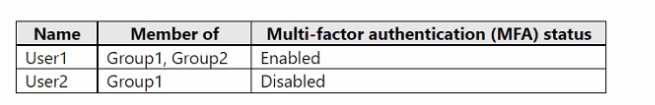
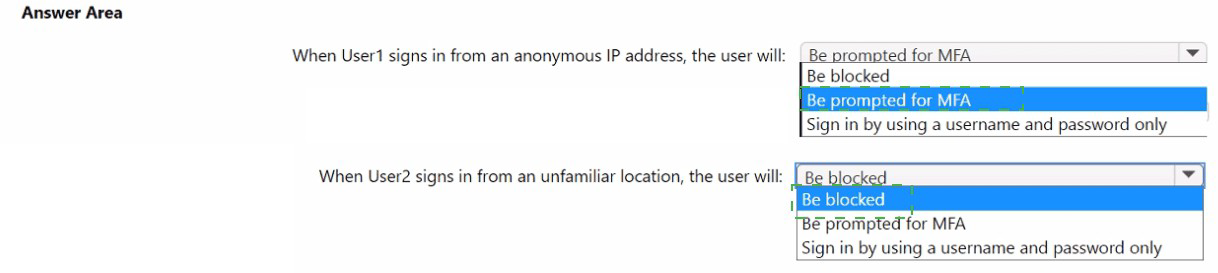
You create and enforce a Microsoft Entra Identity Protection sign-in risk policy that has the
following settings:
• Assignments: Include Group1, exclude Group2
• Conditions: Sign-in risk level: Low and above
• Access: Allow access, Require multi-factor authentication
You need to identify what occurs when the users sign in to Microsoft Entra ID.
What should you identify for each user? To answer, select the appropriate options in the
answer area.
NOTE: Each correct selection is worth one point.
You have an on-premises datacenter.
You have an Azure subscription that contains a virtual machine named VM1. VM1 is
connected to a virtual network named VNet1. VNet1 is connected to the on-premises
datacenter by using a Site-to-Site (S2S) VPN.
You plan to create an Azure storage account named storage1 and App1.
You need to ensure that network communication to each resource meets the following
requirements:
• Connections to App1 must be allowed only from corporate network NAT addresses.
• Connections from VNet1 to storage1 must use the Microsoft backbone network.
• The solution must minimize costs.
What should you configure for each resource? To answer, drag the appropriate
components to the correct resources. Each component may be used once, more than
once, or not at all. You may need to drag the split bar between panes or scroll to view
content.
NOTE: Each correct selection is worth one point.


O: 12 HOTSPOT
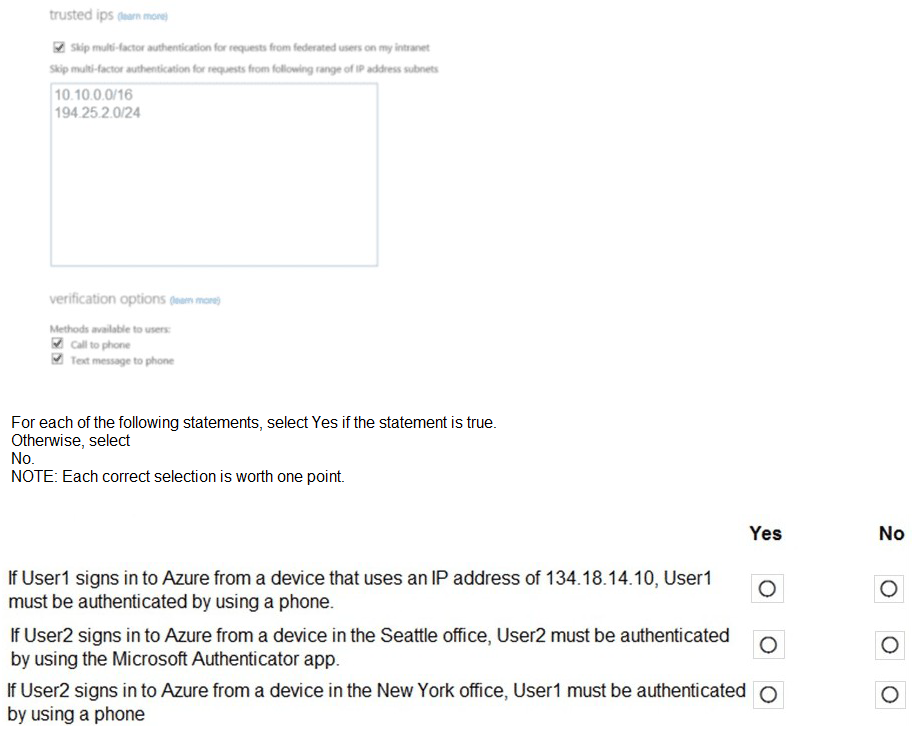
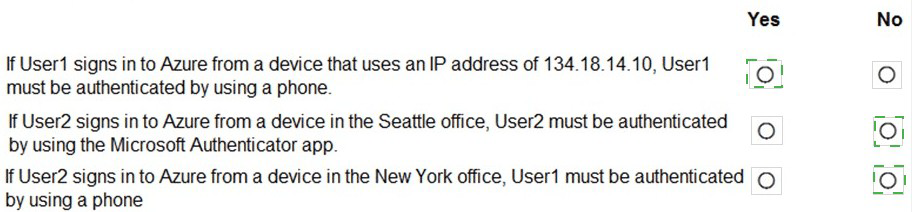
Your company has two offices in Seattle and New York. Each office connects to the
Internet by using a NAT device. The offices use the IP addresses shown in the following
table.
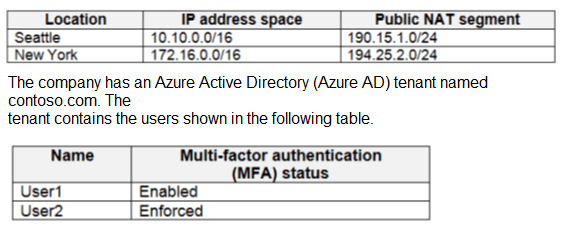
The MFA service settings are configured as shown in the exhibit. (Click the Exhibit tab.)
You have an Azure subscription that contains the resources shown in the following table.
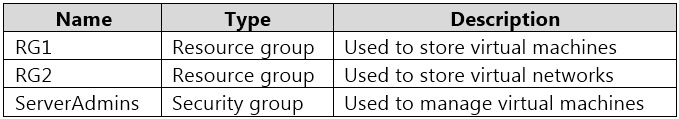
You need to ensure that ServerAdmins can perform the following tasks:
Create virtual machines in RG1 only.
Connect the virtual machines to the existing virtual networks in RG2 only.
The solution must use the principle of least privilege.
Which two role-based access control (RBAC) roles should you assign to ServerAdmins?
Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
A. a custom RBAC role for RG2
B. the Network Contributor role for RG2
C. the Contributor role for the subscription
D. a custom RBAC role for the subscription
E. the Network Contributor role for RG1
F. the Virtual Machine Contributor role for RG1
You have 10 on-premises servers that run Windows Server 2019.
You plan to implement Azure Security Center vulnerability scanning for the servers.
What should you install on the servers first?
A. the Security Events data connector in Azure Sentinel
B. the Microsoft Endpoint Configuration Manager client
C. the Azure Arc enabled servers Connected Machine agent
D. the Microsoft Defender for Endpoint agent
Lab Task
use the following login credentials as needed:
To enter your username, place your cursor in the Sign in box and click on the username
below.
To enter your password. place your cursor in the Enter password box and click on the
password below.
Azure Username: Userl -28681041@ExamUsers.com
Azure Password: GpOAe4@lDg
If the Azure portal does not load successfully in the browser, press CTRL-K to reload the
portal in a new browser tab.
The following information is for technical support purposes only:
Lab Instance: 28681041
Task 9
You need to ensure that the rg1lod28681041n1 Azure Storage account is encrypted by
using a key stored in the KeyVault28681041 Azure key vault.
Explanation:
To configure rg1lod28681041n1 Azure Storage Account to use a customer-managed key (CMK) from KeyVault28681041, first sign in to the Azure Portal with the provided credentials, then ensure KeyVault28681041 has soft delete and purge protection enabled, along with an access policy granting key permissions (Get, Wrap, Unwrap). Next, create or select an existing encryption key (e.g., RSA 2048-bit) in the key vault. In the storage account’s Encryption settings, switch to Customer-managed keys, select KeyVault28681041 as the key source, and choose the appropriate key. Finally, save the changes and verify in the Encryption blade that the storage account now uses the key vault key for encryption. If access issues arise, check key vault firewall rules, cross-subscription permissions, or RBAC roles (e.g., Key Vault Crypto Officer).
Your company has an Azure subscription named Sub1 that is associated to an Azure
Active Directory Azure (Azure AD) tenant named contoso.com.
The company develops a mobile application named App1. App1 uses the OAuth 2 implicit
grant type to acquire Azure AD access tokens.
You need to register App1 in Azure AD.
What information should you obtain from the developer to register the application?
A. a redirect URI
B. a reply URL
C. a key
D. an application ID
You are troubleshooting a security issue for an Azure Storage account You enable Azure Storage Analytics logs and archive It to a storage account. What should you use to retrieve the diagnostics logs?
A. Azure Storage Explorer
B. SQL query editor in Azure
C. Azure Monitor
D. Azure Cosmos DB explorer
You plan to deploy Azure container instances.
You have a containerized application that validates credit cards. The application is
comprised of two
containers: an application container and a validation container.
The application container is monitored by the validation container. The validation container
performs security checks by making requests to the application container and waiting for
responses after every transaction.
You need to ensure that the application container and the validation container are
scheduled to be deployedtogether. The containers must communicate to each other only
on ports that are not externally exposed.
What should you include in the deployment?
A. application security groups
B. network security groups (NSGs)
C. management groups
D. container groups
You have an Azure subscription that contains the resources show in the following table.
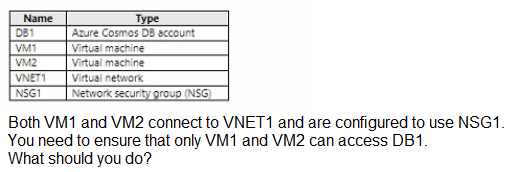
A. Add the IP address range of VNET1 to the Firewall setting of DB1.
B. For NSG1, configure a rule that has a service tag.
C. Create an application security group.
D. Configure DB1 to allow access from only VNET1
From Azure Security Center, you enable Azure Container Registry vulnerability scanning of
the images in
Registry1.
You perform the following actions:
Push a Windows image named Image1 to Registry1.
Push a Linux image named Image2 to Registry1.
Push a Windows image named Image3 to Registry1.
Modify Image1 and push the new image as Image4 to Registry1.
Modify Image2 and push the new image as Image5 to Registry1.
Which two images will be scanned for vulnerabilities? Each correct answer presents a
complete solution.
NOTE: Each correct selection is worth one point.
A. Image4
B. Image2
C. Image1
D. Image3
E. Image5
| Page 7 out of 42 Pages |
| Previous |