Topic 4: Mix Questions
You have an Azure subscription named Subscription1.
You deploy a Linux virtual machine named VM1 to Subscription1.
You need to monitor the metrics and the logs of VM1.
D18912E1457D5D1DDCBD40AB3BF70D5D
What should you use?
A. the AzurePerformanceDiagnostics extension
B. Azure HDInsight
C. Linux Diagnostic Extension (LAD) 3.0
D. Azure Analysis Services
You have an Azure subscription linked to an Azure Active Directory Premium Plan 1 tenant.
You plan to implement Azure Active Directory (Azure AD) Identity Protection.
You need to ensure that you can configure a user risk policy and a sign-in risk policy.
What should you do first?
A. Purchase Azure Active Directory Premium Plan 2 licenses for all users.
B. Register all users for Azure Multi-Factor Authentication (MFA).
C. Enable security defaults for Azure AD.
D. Upgrade Azure Security Center to the standard tier.
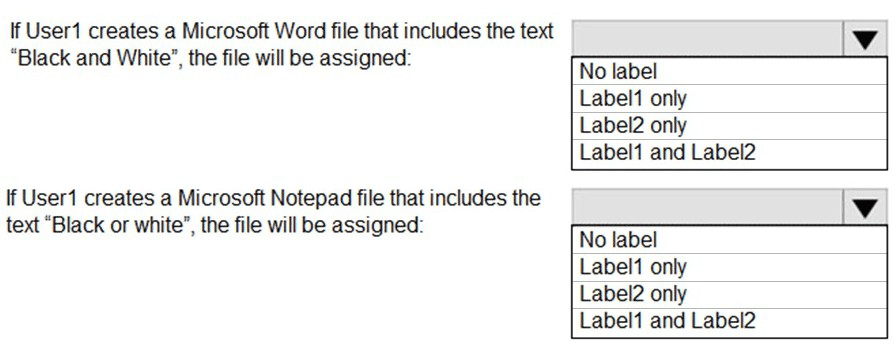
You have the Azure Information Protection conditions shown in the following table.
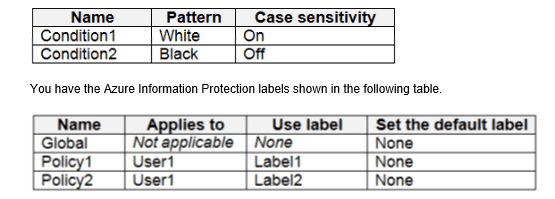
You need to identify how Azure Information Protection will label files.
What should you identify? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have an Azure subscription that uses Microsoft Defender for Cloud.
You have an Amazon Web Service (AWS) account named AWS1 that is connected to
defender for Cloud.
You need to ensure that AWS foundational Security Best Practices. The solution must
minimize administrate effort.
What should do you in Defender for Cloud?
A. Create a new customer assessment.
B. Assign a built-in assessment.
C. Assign a built-in compliance standard.
D. Create a new custom standard.
Note: The question is included in a number of questions that depicts the identical
set-up. However, every question has a distinctive result. Establish if the solution
satisfies the requirements.
Your company has an Active Directory forest with a single domain, named
weylandindustries.com. They also have an Azure Active Directory (Azure AD) tenant with
the same name.
You have been tasked with integrating Active Directory and the Azure AD tenant. You
intend to deploy Azure AD Connect.
Your strategy for the integration must make sure that password policies and user logon
limitations affect user accounts that are synced to the Azure AD tenant, and that the
amount of necessary servers are reduced.
Solution: You recommend the use of federation with Active Directory Federation Services
(AD FS).
Does the solution meet the goal?
A. Yes
B. No
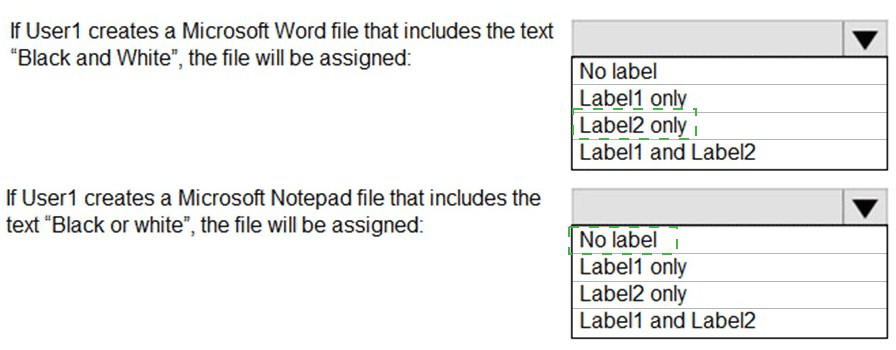
You have an Azure subscription that contains the virtual networks shown in the following
table.
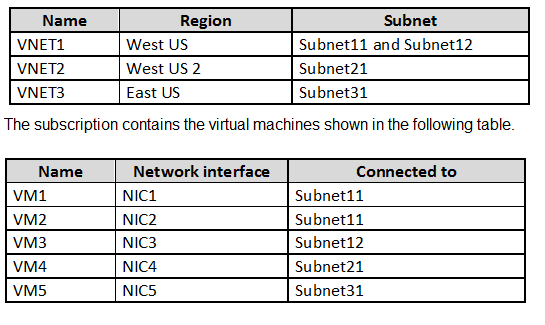
On NIC1, you configure an application security group named ASG1.
On which other network interfaces can you configure ASG1?
A. NIC2 only
B. NIC2, NIC3, NIC4, and NIC5
C. NIC2 and NIC3 only
D. NIC2, NIC3, and NIC4 only
You have 15 Azure virtual machines in a resource group named RG1.
All virtual machines run identical applications.
You need to prevent unauthorized applications and malware from running on the virtual
machines.
What should you do?
A. Configure Azure Active Directory (Azure AD) Identity Protection.
B. From Microsoft Defender for Cloud, configure adaptive application controls.
C. Apply an Azure policy to RGI.
D. Apply a resource lock to RGI.
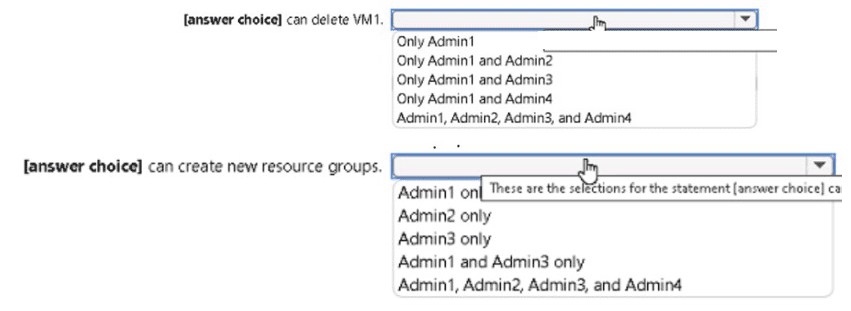
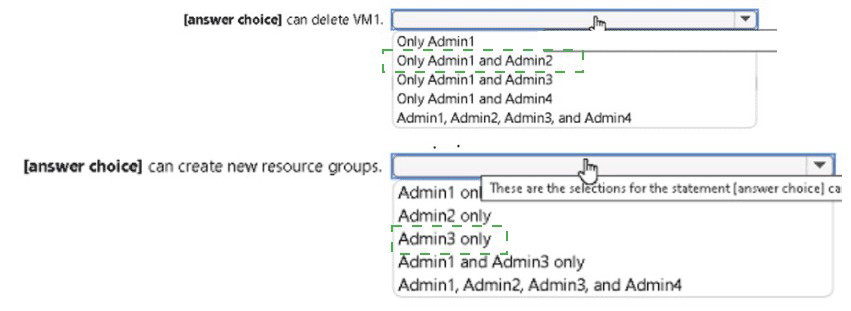
You have the role assignments shown in the following exhibit.

Use the drop-down menus to select the answer choice that completes each statement
based on the information presented in the graphic.
NOTE: Each correct selection is worth one point.
You have an Azure Active Directory (Azure AD) tenant.
You have the deleted objects shown in the following table.
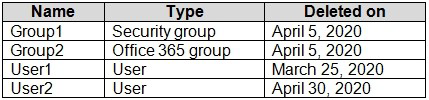
On May 4, 2020, you attempt to restore the deleted objects by using the Azure Active
Directory admin center.
Which two objects can you restore? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
A. Group1
B. Group2
C. User2
D. User1
You have an Azure subscription named Sub1 that uses Microsoft Defender for Cloud. You
have the management group hierarchy shown in the following exhibit.
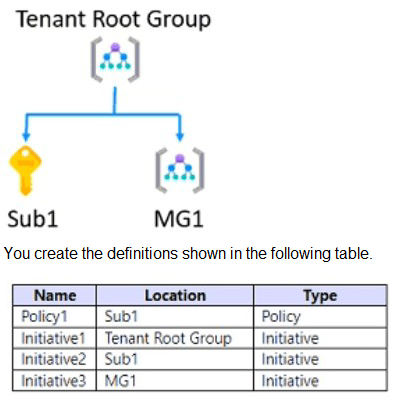
You need to use Defender for Cloud to add a security policy. Which definitions can you use
as a security policy?
A. Policy1 only
B. Policy1 and Initiative1 only
C. Initiative1 and Initiative2 only
D. Initiative1, Initiative2, and Initiatives only
E. Policy1, Initiative1, Initiative2, and Initiative3
You have an Azure subscription that is linked to an Azure Active Directory (Azure AD)
tenant.
From the Azure portal, you register an enterprise application.
Which additional resource will be created in Azure AD?
A. a service principal
B. an X.509 certificate
C. a managed identity
D. a user account
You have an Azure subscription that contains an Azure SQL database named DB1 in the
East US Azure region. You create the storage accounts shown in the following table.
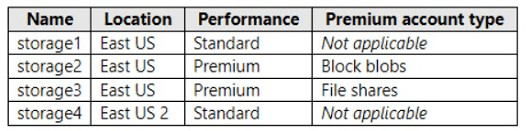
You plan to enable auditing for DB1.
Which storage accounts can you use as the auditing destination for DB1?
A. storage1 only
B. storage1 and storage4 only
C. Storage2 and storage3 only
D. storage1, storage2 and storage3 only
| Page 14 out of 42 Pages |
| Previous |